July 15th, 2022
2 min read
As the digital transformation of society and industries further accelerates, the rise of security breaches and intrusions continues. Supply chain security risks are increasing with cybercriminals gaining access through unauthorized software related to procurements, maintenance and operations of network devices and ICT infrastructures. Organizations are faced with the challenge of detecting and reducing security risks across the supply chain before they bring on world-wide havoc based on severe security incidents. Then there’s also the matter of that how to trust their products and services between suppliers and customers. Is there a way to secure shared system configurations and network devices?
NTT and NEC are creating a more trusted and secure supply chain network through a new security transparency assurance innovation.

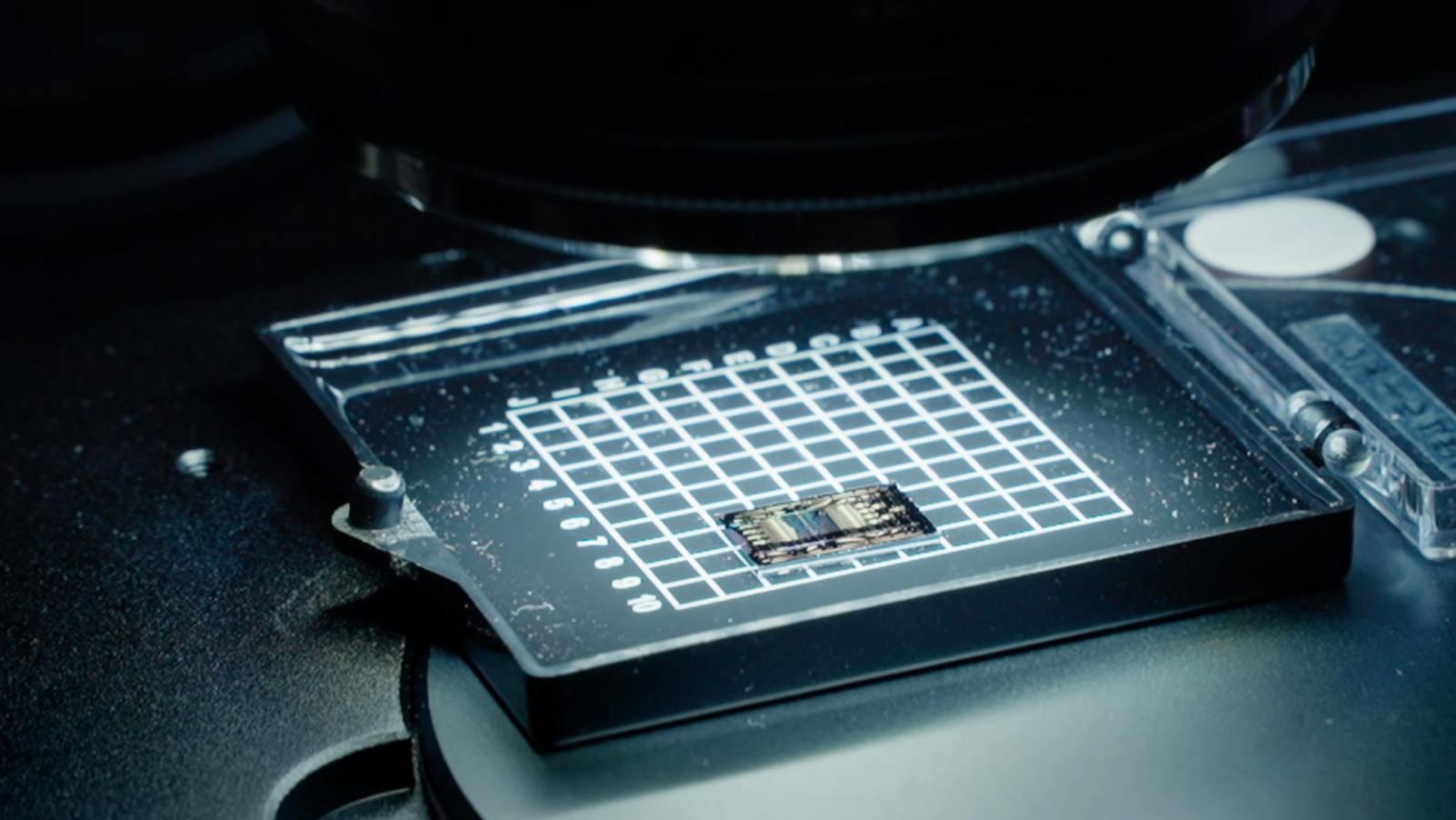
We are leveraging IOWN’s photonics-electronics convergence technology and 5G to solve the security problems of decentralized, remote computers.
Decentralization increases the risk of malicious software and hardware vulnerabilities, making it harder to gain visibility and inspect computer devices spread across multiple locations.
Security risk reduction technology for ICT infrastructure
Research and development have been done to discover new ways to analyze the software configuration of telecommunication equipment and a backdoor inspection technology for detecting illegal functions in software. This new technology works in three ways:
-
Visualizing software configurations in the network devices continuously across a supply chain (e.g., manufacturing, shipping, deployment and operations) generates the device information, including the inspection results of backdoors and illegal components.
-
The device information enables high-quality risk analysis and monitoring that’s complete and accurate, providing transparency of the device information at high levels through continuous updates.
-
Sharing the device information across the supply chain enables any one organization to take countermeasures against risks, increase visibility and improve security at all levels.
It means we can now inspect communications equipment from afar and match device-specification data with operation data to detect out-of-spec behavior. The team has achieved this type of detection by directly analyzing the binary code inside a device. The new technology will allow for more versatile, secure, and high-performance networks of software and hardware supplied by multiple vendors to become the next generation of communication devices.

NTT calls these high-performance general-purpose devices ‘super-white-boxes’, which can be applied to various IOWN communication-infrastructure devices in different circumstances.
Customers can quickly check the presence of suspicious components by referring to the device information during its product lifecycle (e.g., designing, producing, procurement, installation and operation), and suppliers can explain the risk of contamination with unauthorized components more objectively. Also, customers will be able to take faster action by identifying risks and impacts using specific device information once a new software vulnerability is found.
Looking ahead
NTT and NEC began working together in June 2020 on joint research and development to support the global rollout of new ICT products on IOWN. We are planning to carry out technical validation studies using this technology to verify the effectiveness of each elemental technology and identify issues. More partners, including communication device vendors, system integrators and user companies, will be needed to construct and operate our vision of more trusted networks and more secure supply chains.